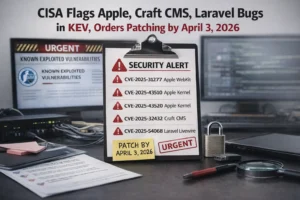
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added five newly identified security vulnerabilities affecting Apple, Craft CMS, and Laravel Livewire to its Known Exploited Vulnerabilities (KEV) catalog. Federal agencies have been instructed to remediate these issues by April 3, 2026, due to active exploitation in the wild.
Actively Exploited Vulnerabilities
The following vulnerabilities are now listed in CISA’s KEV catalog:
- CVE-2025-31277 (CVSS 8.8) – A WebKit memory corruption flaw in Apple devices that can be triggered through malicious web content. (Patched: July 2025)
- CVE-2025-43510 (CVSS 7.8) – A kernel-level memory corruption issue that could allow unintended memory modifications across processes. (Patched: December 2025)
- CVE-2025-43520 (CVSS 8.8) – Another Apple kernel vulnerability that may lead to system crashes or arbitrary kernel memory writes. (Patched: December 2025)
- CVE-2025-32432 (CVSS 10.0) – A critical code injection flaw in Craft CMS enabling remote code execution. (Patched: April 2025)
- CVE-2025-54068 (CVSS 9.8) – A Laravel Livewire vulnerability that allows unauthenticated attackers to execute remote commands under certain conditions. (Patched: July 2025)
iOS Exploit Chain and Malware Campaigns
The inclusion of Apple vulnerabilities follows reports from security researchers, including Google Threat Intelligence Group (GTIG), iVerify, and Lookout. These flaws are reportedly part of an iOS exploit chain known as “DarkSword,” which has been used to deploy malware families such as GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER for data exfiltration.
Craft CMS Zero-Day Exploitation
The Craft CMS vulnerability (CVE-2025-32432) is believed to have been exploited as a zero-day since February 2025. Security researchers have linked its exploitation to a threat group known as Mimo (also called Hezb), which has used the flaw to deploy cryptocurrency miners and residential proxyware.
Laravel Vulnerability Linked to MuddyWater Attacks
The Laravel Livewire flaw (CVE-2025-54068) has been associated with campaigns conducted by the Iranian state-sponsored group MuddyWater (aka Boggy Serpens). According to threat intelligence reports, the group has targeted sectors such as energy, maritime, finance, and diplomatic organizations.
Security researchers highlight that MuddyWater is evolving its tactics by combining:
- Social engineering campaigns
- AI-enhanced malware
- Advanced persistence mechanisms
The group also leverages a custom-built platform to automate phishing campaigns at scale while maintaining control over targets and sender identities.
Ongoing Campaigns and Targeted Attacks
Recent activity attributed to MuddyWater includes a prolonged attack campaign against a national energy and maritime organization in the UAE between August 2025 and February 2026. The operation involved multiple attack waves and deployment of malware such as:
- GhostBackDoor
- Nuso (HTTP_VIP)
- UDPGangster
- LampoRAT (CHAR)
The group is also known for abusing trusted accounts from government and corporate entities to bypass security filters and deliver malicious payloads.
Urgent Action Required
CISA has emphasized that all federal agencies must apply the necessary patches by the April 3 deadline to mitigate risks associated with these actively exploited vulnerabilities. Organizations outside the federal ecosystem are strongly advised to follow suit immediately.